Trans-Compiler based Mobile Applications code converter: Swift to java
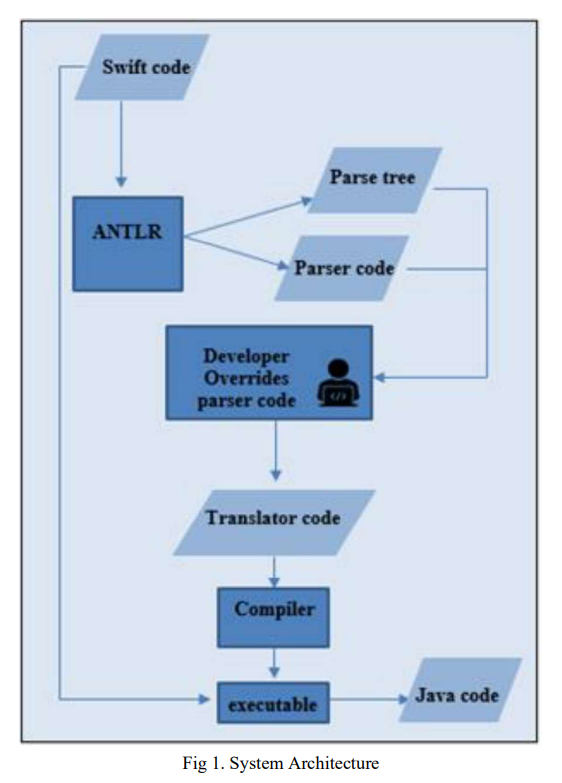
Numerous commercial tools like Xamarin, React Native and PhoneGap utilize the concept of cross-platform mobile applications development that builds applications once and runs it everywhere opposed to native mobile app development that writes in a specific programming language for every platform. These commercial tools are not very efficient for native developers as mobile applications must be written in specific language and they need the usage of specific frameworks. In this paper, a suggested approach in TCAIOSC tool to convert mobile applications from Android to iOS is used to develop the
In-silico development and assessment of a Kalman filter motor decoder for prosthetic hand control
Up to 50% of amputees abandon their prostheses, partly due to rapid degradation of the control systems, which require frequent recalibration. The goal of this study was to develop a Kalman filter-based approach to decoding motoneuron activity to identify movement kinematics and thereby provide stable, long-term, accurate, real-time decoding. The Kalman filter-based decoder was examined via biologically varied datasets generated from a high-fidelity computational model of the spinal motoneuron pool. The estimated movement kinematics controlled a simulated MuJoCo prosthetic hand. This clear-box
Improved strain measuring using fast strain-encoded cardiac MR
The strain encoding (SENC) technique encodes regional strain of the heart into the acquired MR images and produces two images with two different tunings so that longitudinal strain, on the short-axis view, or circumferential strain on the long-axis view, are measured. Interleaving acquisition is used to shorten the acquisition time of the two tuned images by 50%, but it suffers from errors in the strain calculations due to inter-tunings motion of the heart, which is the motion between two successive acquisitions. In this work, a method is proposed to correct for the inter-tunings motion by
Improved technique to detect the infarction in delayed enhancement image using k-mean method
Cardiac magnetic resonance (CMR) imaging is an important technique for cardiac diagnosis. Measuring the scar in myocardium is important to cardiologists to assess the viability of the heart. Delayed enhancement (DE) images are acquired after about 10 minutes following injecting the patient with contrast agent so the infracted region appears brighter than its surroundings. A common method to segment the infarction from DE images is based on intensity Thresholding. This technique performed poorly for detecting small infarcts in noisy images. In this work we aim to identify the best threshold
Inherent fat cancellation in complementary spatial modulation of magnetization
An efficient fat suppression method is presented for MR tagging with complementary spatial modulation of magnetization (CSPAMM). In this method, the complementary modulation is applied to the water content of the tissues, while in-phase modulation is applied to the fat content. Therefore, during image reconstruction, the subtraction of the acquired images increases the tagging contrast of the water while cancels the tagging lines of the fat. Compared with the existing fat suppression techniques, the proposed method allows imaging with higher temporal resolution and shorter echo-time without
Improved estimation of the cardiac global function using combined long and short axis MRI images of the heart
Background: Estimating the left ventricular (LV) volumes at the different cardiac phases is necessary for evaluating the cardiac global function. In cardiac magnetic resonance imaging, accurate estimation of the LV volumes requires the processing a relatively large number of parallel short-axis cross-sectional images of the LV (typically from 9 to 12). Nevertheless, it is inevitable sometimes to estimate the volume from a small number of cross-sectional images, which can lead to a significant reduction of the volume estimation accuracy. This usually encountered when a number of cross-sectional
New feature splitting criteria for co-training using genetic algorithm optimization
Often in real world applications only a small number of labeled data is available while unlabeled data is abundant. Therefore, it is important to make use of unlabeled data. Co-training is a popular semi-supervised learning technique that uses a small set of labeled data and enough unlabeled data to create more accurate classification models. A key feature for successful co-training is to split the features among more than one view. In this paper we propose new splitting criteria based on the confidence of the views, the diversity of the views, and compare them to random and natural splits. We
New approach for data acquisition and image reconstruction in parallel magnetic resonance imaging
In this study, we propose a novel data acquisition and image reconstruction method for parallel magnetic resonance imaging (MRI). The proposed method improves the GRAPPA algorithm by simultaneously collecting data using the body coil in addition to localized surface coils. The body coil data is included in the GRAPPA reconstruction as an additional coil. The reconstructed body coil image shows greater uniformity over the field of view than the conventional sum-of-squares (SoS) reconstruction that is conventionally used with GRAPPA. The body coil image can also be used to correct for spatial
In silico design and experimental validation of sirnas targeting conserved regions of multiple hepatitis c virus genotypes
RNA interference (RNAi) is a post-transcriptional gene silencing mechanism that mediates the sequence-specific degradation of targeted RNA and thus provides a tremendous opportunity for development of oligonucleotide-based drugs. Here, we report on the design and validation of small interfering RNAs (siRNAs) targeting highly conserved regions of the hepatitis C virus (HCV) genome. To aim for therapeutic applications by optimizing the RNAi efficacy and reducing potential side effects, we considered different factors such as target RNA variations, thermodynamics and accessibility of the siRNA
Myocardium segmentation in strain-encoded (SENC) magnetic resonance images using graph-cuts
Evaluation of cardiac functions using Strain Encoded (SENC) magnetic resonance (MR) imaging is a powerful tool for imaging the deformation of left and right ventricles. However, automated analysis of SENC images is hindered due to the low signal-to-noise ratio SENC images. In this work, the authors propose a method to segment the left and right ventricles myocardium simultaneously in SENC-MR short-axis images. In addition, myocardium seed points are automatically selected using skeletonisation algorithm and used as hard constraints for the graph-cut optimization algorithm. The method is based
Pagination
- Previous page ‹‹
- Page 9
- Next page ››