Symmetric encryption algorithms using chaotic and non-chaotic generators: A review
This paper summarizes the symmetric image encryption results of 27 different algorithms, which include substitution-only, permutation-only or both phases. The cores of these algorithms are based on several discrete chaotic maps (Arnold's cat map and a combination of three generalized maps), one continuous chaotic system (Lorenz) and two non-chaotic generators (fractals and chess-based algorithms). Each algorithm has been analyzed by the correlation coefficients between pixels (horizontal, vertical and diagonal), differential attack measures, Mean Square Error (MSE), entropy, sensitivity
Synthesis of a family of differential cross-coupled oscillators and design application
A new class of differential oscillators comprising ten possible circuits is introduced in this work. Half of the members of this family are LC-based oscillators and the other half are RC-based ones. While all oscillators are second-order, a maximum of four resistors was imposed as a restriction on possible oscillators that belong to the proposed architecture. Only two of the found oscillators are canonical but all members of the this family have unique and attractive design features. Experimental results using discrete components verify the operation of selected circuits designed for short
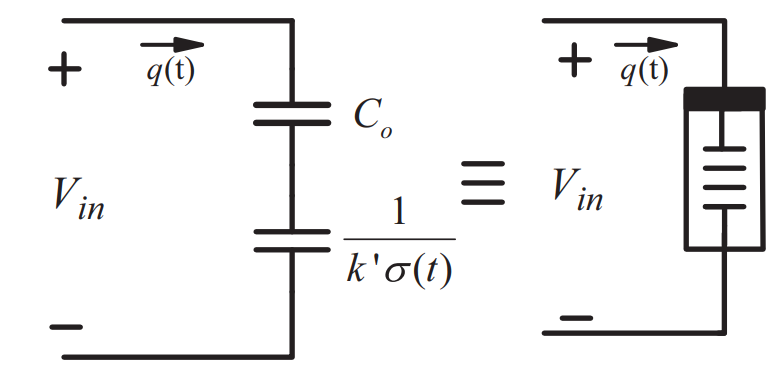
Memcapacitor response under step and sinusoidal voltage excitations
Recently, mem-elements have become fundamental in the circuit theory through promising potential applications based on the built-in memory-properties of these elements. In this paper, the mathematical analysis of the memcapacitor model is derived and the effect of different voltage excitation signals is studied for the linear dopant model. General closed form expressions and analyses are presented to describe the memcapacitor behavior under DC step and sinusoidal voltage excitations. Furthermore, the step and sinusoidal responses are used to analyze the memcapacitor response under any periodic
High-Frequency Capacitorless Fractional-Order CPE and FI Emulator
A fractional-order capacitor and inductor emulator, implemented using MOS transistors, instead of passive capacitors, is introduced in this paper. This is achieved using current mirrors as active elements, without passive resistors, and therefore reducing the circuit complexity and resulting in both a resistorless and capacitorless topology. The emulator has been designed by combining fractional-order differentiator or integrator topologies with a voltage-to-current converter. An important benefit from the design flexibility point of view is that the same topology could be used for emulating a
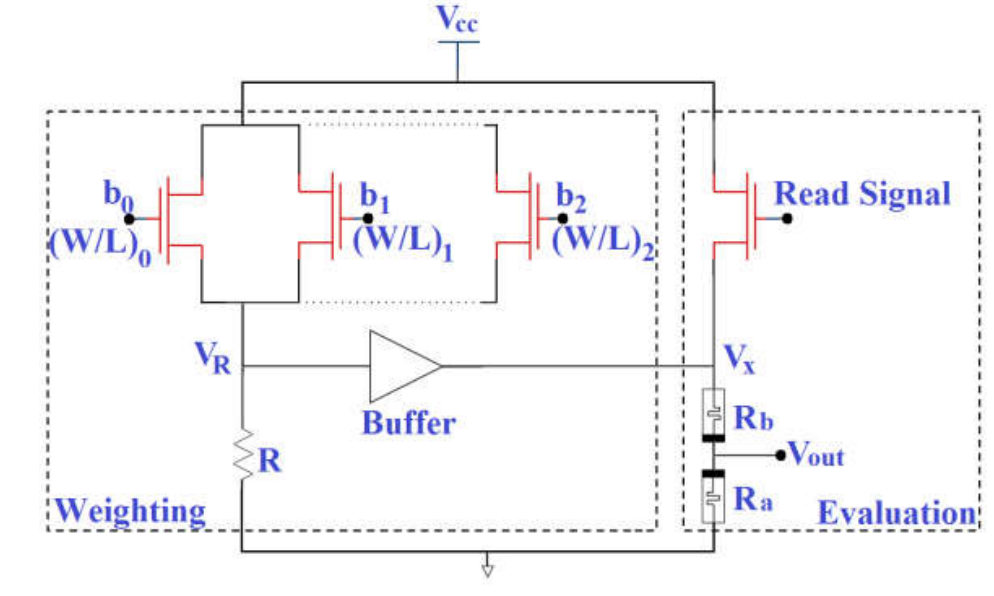
Memristor-based data converter circuits
This paper introduces data converter circuit based on memristors. A proposed Digital to Analog Converter (DAC) circuit based on non-overlapped input signals, which is suitable for common source connected transistors. Analytical formulas are introduced to relate the digital input with the analog output including the transistors dimension. In addition, PSpice simulations are performed to validate the theoretical analysis for several cases. Moreover, a modified circuit for 2-bit digital to analog converter is introduced where the input can be overlapped. One of the advantages of these designs
Hardware Optimized FPGA Implementations of High-Speed True Random Bit Generators Based on Switching-Type Chaotic Oscillators
One of the important applications of chaotic oscillators is their employment as sources of entropy for True Random Bit Generators (TRBGs). In this work, we introduce high-speed TRBGs realized on a modular Field Programmable Gate Array (FPGA) hardware platform using two different switching-type chaotic oscillators. While both oscillators are autonomous, one is 3-D and the other is 4-D. This enables us to investigate and compare the advantages/disadvantages of higher dimensional chaotic oscillators on the throughput, hardware requirements and security of the generated bit-streams. For that
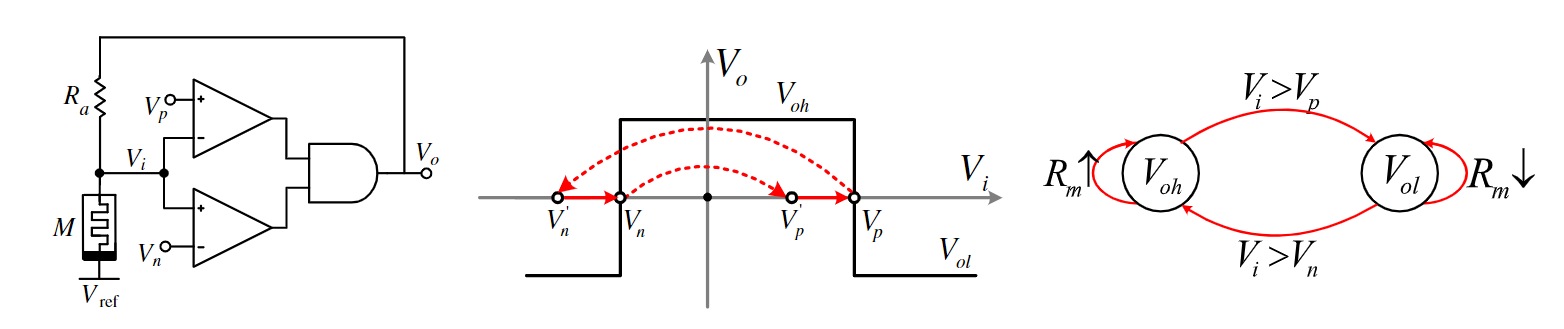
Memristor-based voltage-controlled relaxation oscillators
This paper introduces two voltage-controlled memristor-based reactance-less oscillators with analytical and circuit simulations. Two different topologies which are R-M and M-R are discussed as a function of the reference voltage where the generalized formulas of the oscillation frequency and conditions for oscillation for each topology are derived. The effect of the reference voltage on the circuit performance is studied and validated through different examples using PSpice simulations. A memristor-based voltage-controlled oscillator (VCO) is introduced as an application for the proposed
FPGA-Based Memristor Emulator Circuit for Binary Convolutional Neural Networks
Binary convolutional neural networks (BCNN) have been proposed in the literature for resource-constrained IoTs nodes and mobile computing devices. Such computing platforms have strict constraints on the power budget, system performance, processing and memory capabilities. Nonetheless, the platforms are still required to efficiently perform classification and matching tasks needed in various applications. The memristor device has shown promising results when utilized for in-memory computing architectures, due to its ability to perform storage and computation using the same physical element
Chaotic system modelling using a neural network with optimized structure
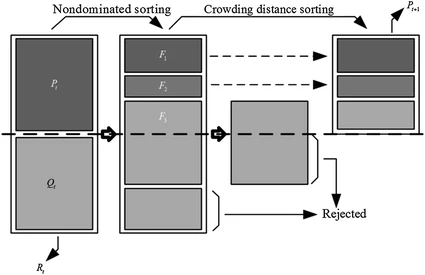
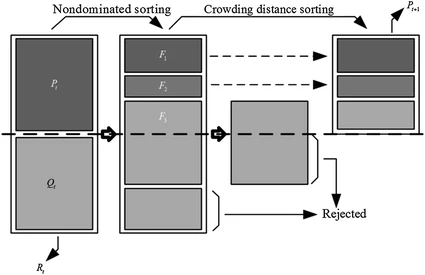
In this work, the Artificial Neural Networks (ANN) are used to model a chaotic system. A method based on the Non-dominated Sorting Genetic Algorithm II (NSGA-II) is used to determine the best parameters of a Multilayer Perceptron (MLP) artificial neural network. Using NSGA-II, the optimal connection weights between the input layer and the hidden layer are obtained. Using NSGA-II, the connection weights between the hidden layer and the output layer are also obtained. This ensures the necessary learning to the neural network. The optimized functions by NSGA-II are the number of neurons in the
Chaotic system modelling using a neural network with optimized structure
In this work, the Artificial Neural Networks (ANN) are used to model a chaotic system. A method based on the Non-dominated Sorting Genetic Algorithm II (NSGA-II) is used to determine the best parameters of a Multilayer Perceptron (MLP) artificial neural network. Using NSGA-II, the optimal connection weights between the input layer and the hidden layer are obtained. Using NSGA-II, the connection weights between the hidden layer and the output layer are also obtained. This ensures the necessary learning to the neural network. The optimized functions by NSGA-II are the number of neurons in the
Pagination
- Previous page ‹‹
- Page 17
- Next page ››