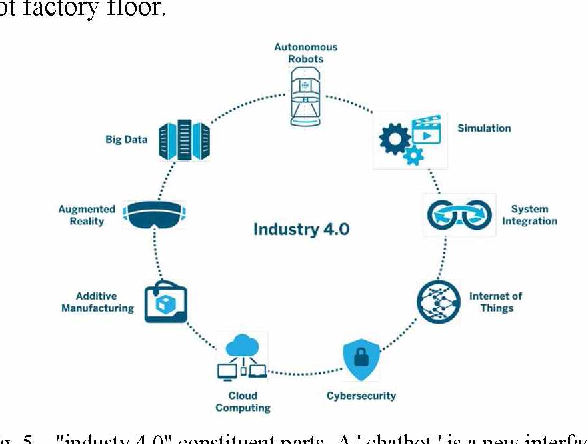
IoT Based AI and its Implementations in Industries
The Internet of Things (IoT) is an Internet revolution that is increasingly used in business, industry, medicine, the economy and other modern information society. IoT, particularly transport, industrial robots and automation systems are supported by artificial intelligence in a wide range of daily implementations with dominant industrial applications. IoT is an interconnected network of physical objects, which enables them to gather and share information, using software, sensor units and network connectivity. In industries; IoT brought about a new revolution in industries. In the field of IoT
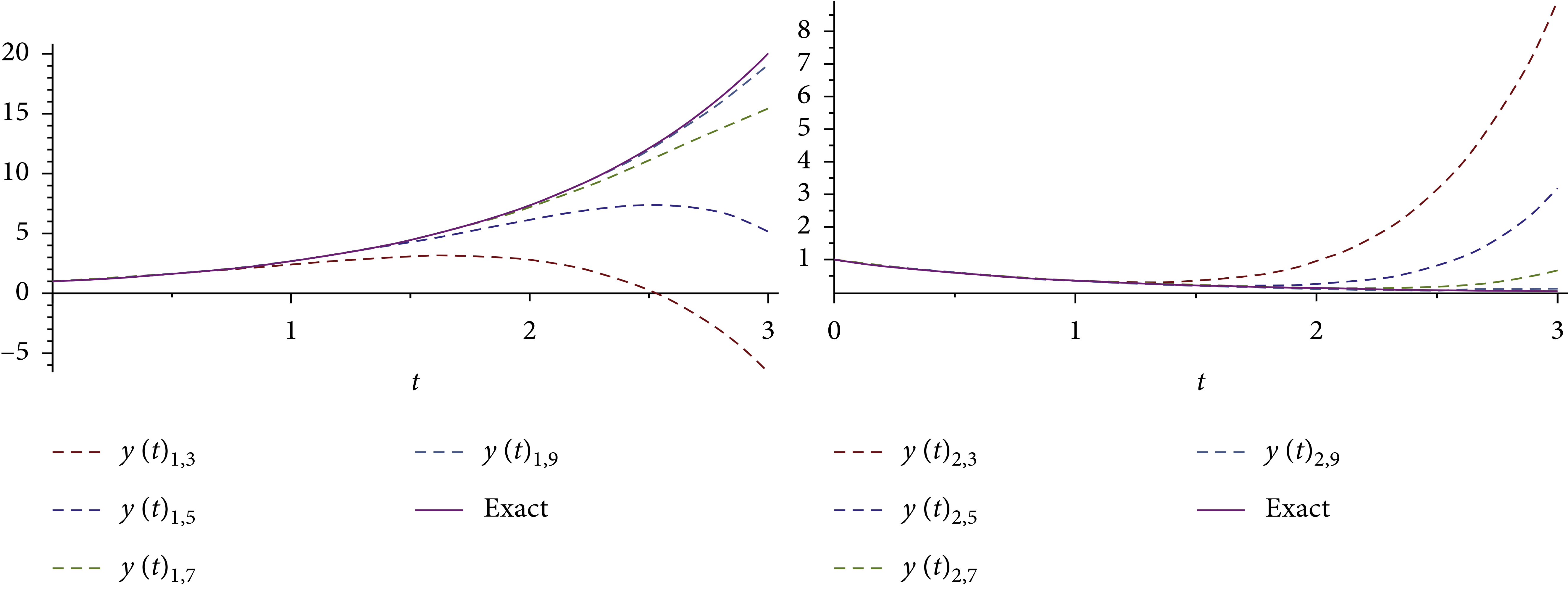
An Analytical Computational Algorithm for Solving a System of Multipantograph DDEs Using Laplace Variational Iteration Algorithm
In this research, an approximation symbolic algorithm is suggested to obtain an approximate solution of multipantograph system of type delay differential equations (DDEs) using a combination of Laplace transform and variational iteration algorithm (VIA). The corresponding convergence results are acquired, and an efficient algorithm for choosing a feasible Lagrange multiplier is designed in the solving process. The application of the Laplace variational iteration algorithm (LVIA) for the problems is clarified. With graphics and tables, LVIA approximates to a high degree of accuracy with a few
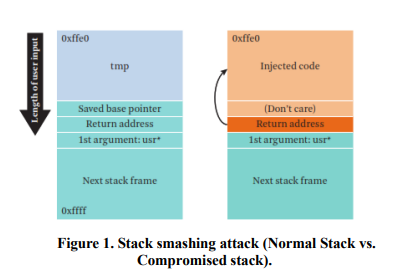
Survey of Code Reuse Attacks and Comparison of Mitigation Techniques
Code-Reuse Attacks (CRAs) are solid mechanisms to bypass advanced software and hardware defenses. Due to vulnerabilities found in software which allows attackers to corrupt the memory space of the vulnerable software to modify maliciously the contents of the memory; hence controlling the software to be able to run arbitrary code. The CRAs defenses either prevents the attacker from reading program code, controlling program memory space directly or indirectly through the usage of pointers. This paper provides a thorough evaluation of the current mitigation techniques against CRAs with regards to
Supporting bioinformatics applications with hybrid multi-cloud services
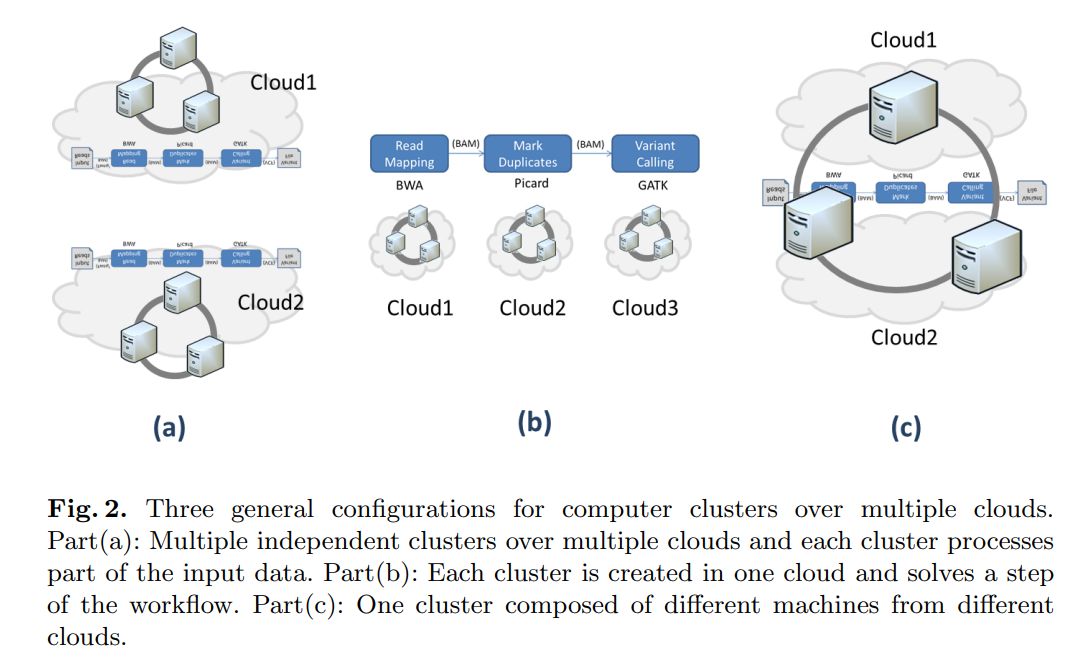
Cloud computing provides a promising solution to the big data problem associated with next generation sequencing applications. The increasing number of cloud service providers, who compete in terms of performance and price, is a clear indication of a growing market with high demand. However, current cloud computing based applications in bioinformatics do not profit from this progress, because they are still limited to just one cloud service provider. In this paper, we present different use case scenarios using hybrid services and resources from multiple cloud providers for bioinformatics
Bivariate Double Density Discrete Wavelet for Enhanced Image Denoising
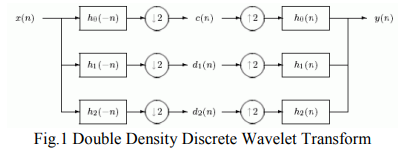
Image denoising is of paramount importance in image processing. In this paper, we propose a new design technique for the design of Double density Discrete Wavelet Transform (DD DWT) AND DD CWT filter bank structure. These filter banks satisfy the perfect reconstruction as well as alias free properties of the DWT. Next, we utilized this filter bank structure in image denoising. Our denoising scheme is based on utilizing the interscale correlation/interscale dependence between wavelet coefficients of a DD DWT of the noisy image. This is known as the Bivariate Shrinkage scheme. More precisely, we
Computing the burrows-wheeler transform of a string and its reverse
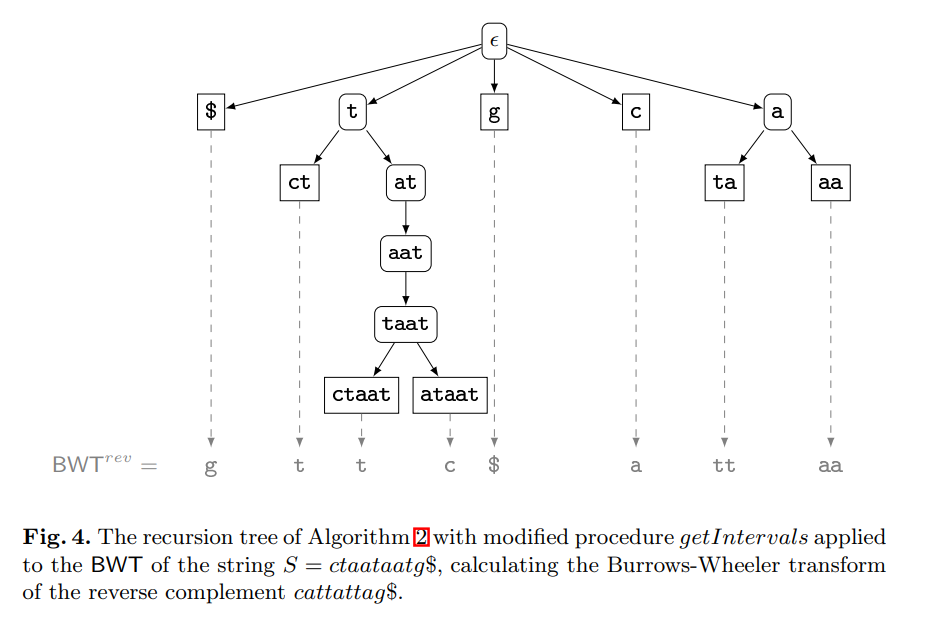
The contribution of this paper is twofold. First, we provide new theoretical insights into the relationship between a string and its reverse: If the Burrows-Wheeler transform (BWT) of a string has been computed by sorting its suffixes, then the BWT and the longest common prefix array of the reverse string can be derived from it without suffix sorting. Furthermore, we show that the longest common prefix arrays of a string and its reverse are permutations of each other. Second, we provide a parallel algorithm that, given the BWT of a string, computes the BWT of its reverse much faster than all
Janitor, certificate and jury (JCJ): Trust scheme for wireless ad-hoc networks
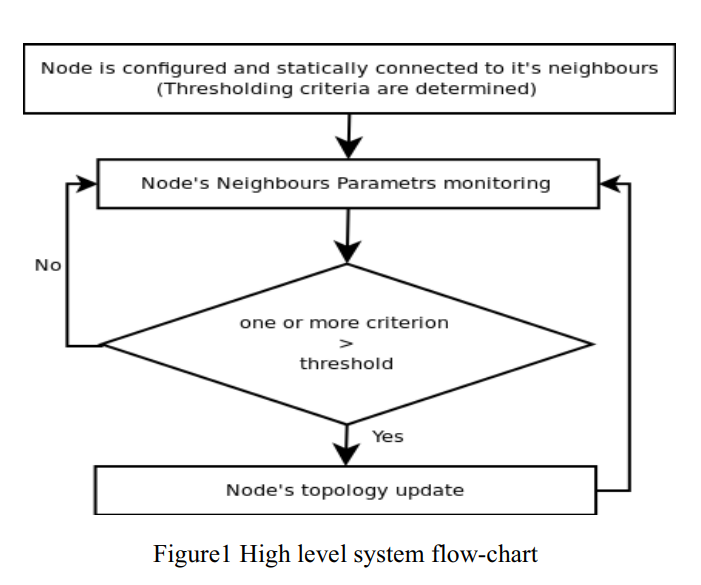
Ad hoc networks are peer mobile nodes that self configure to form a network. In these types of networks there is no routing infrastructure, and usually nodes have limited resources. This imposes a serious problem due to some nodes' selfishness and willingness to preserve their resources. Many approaches have been proposed to deal with this problem and mitigate the selfishness; amongst these approaches are reputation systems. This paper proposes a reputation system scheme that helps isolating misbehaving nodes and decreasing their ability to launch an attack on the network. The idea of this
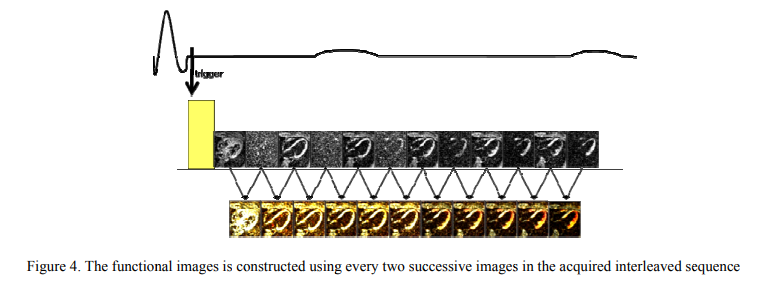
Strain correction in interleaved strain-encoded (SENC) cardiac MR
The strain encoding (SENC) technique directly encodes regional strain of the heart into the acquired MR images and produces two images with two different tunings so that longitudinal strain, on the short-axis view, or circumferential strain on the long-axis view, are measured. Interleaving acquisition is used to shorten the acquisition time of the two tuned images by 50%, but it suffers from errors in the strain calculations due to inter-tunings motion of the heart. In this work, we propose a method to correct for the inter-tunings motion by estimating the motion-induced shift in the spatial
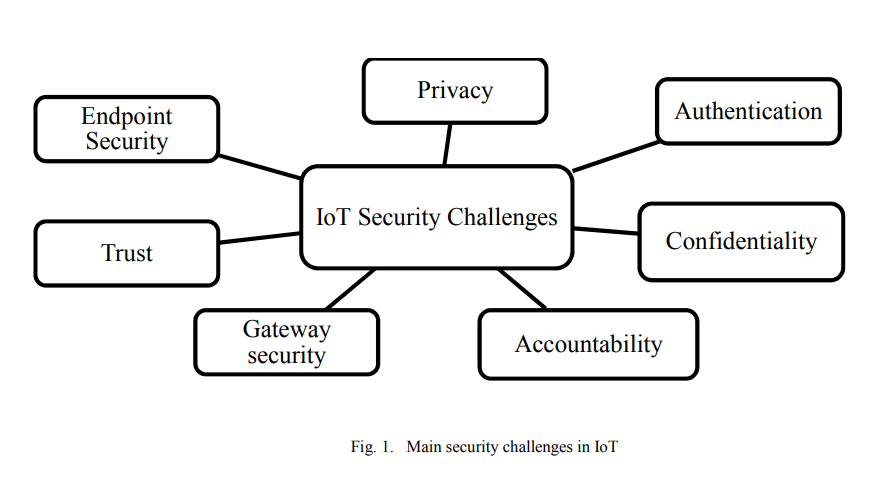
Internet of Things security framework
For the past decade, Internet of Things (IoT) had an important role in our lives. It connects a large number of embedded devices. These devices fulfill very difficult and complicated tasks, which facilitate our work. Till now the security of IoT faces many challenges such as privacy, authentication, confidentiality, trust, middleware security, mobile security and policy enforcement. In order to provide a secure environment for IoT, this paper proposes a framework for IoT devices. © 2017 IEEE.
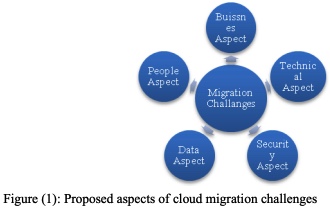
A dynamic system development method for startups migrate to c loud
Cloud computing has become the most convenient environment for startups to run, build and deploy their products. Most startups work on availing platforms as a solution for problems related to education, health, traffic and others. Many of these platforms are mobile applications. With platforms as a service (PaaS), startups can provision their applications and gain access to a suite of IT infrastructure as their business needs. But, startups face many business and technical challenges to adapt rapidly to cloud computing. This paper helps startups to build a migration strategy. It discusses
Pagination
- Previous page ‹‹
- Page 26
- Next page ››